When Privacy Backfires: Signal, Government Communications, and the Case for Controlled Systems

218
By Will Elkadi, Public Interest Technology Advocate and CEO of eLab Communications
In a world where the United States heavily relies on technology, artificial intelligence, and human operatives to ensure peace, prosperity, and security, the need for bulletproof communication systems is paramount. The stakes are immense, with national security hinging on the integrity of every digital exchange. While commercially available secure messaging apps like Signal have gained widespread trust, a growing body of evidence suggests they fall short when used for the most sensitive government communications.
When Human Error Undermines Encryption
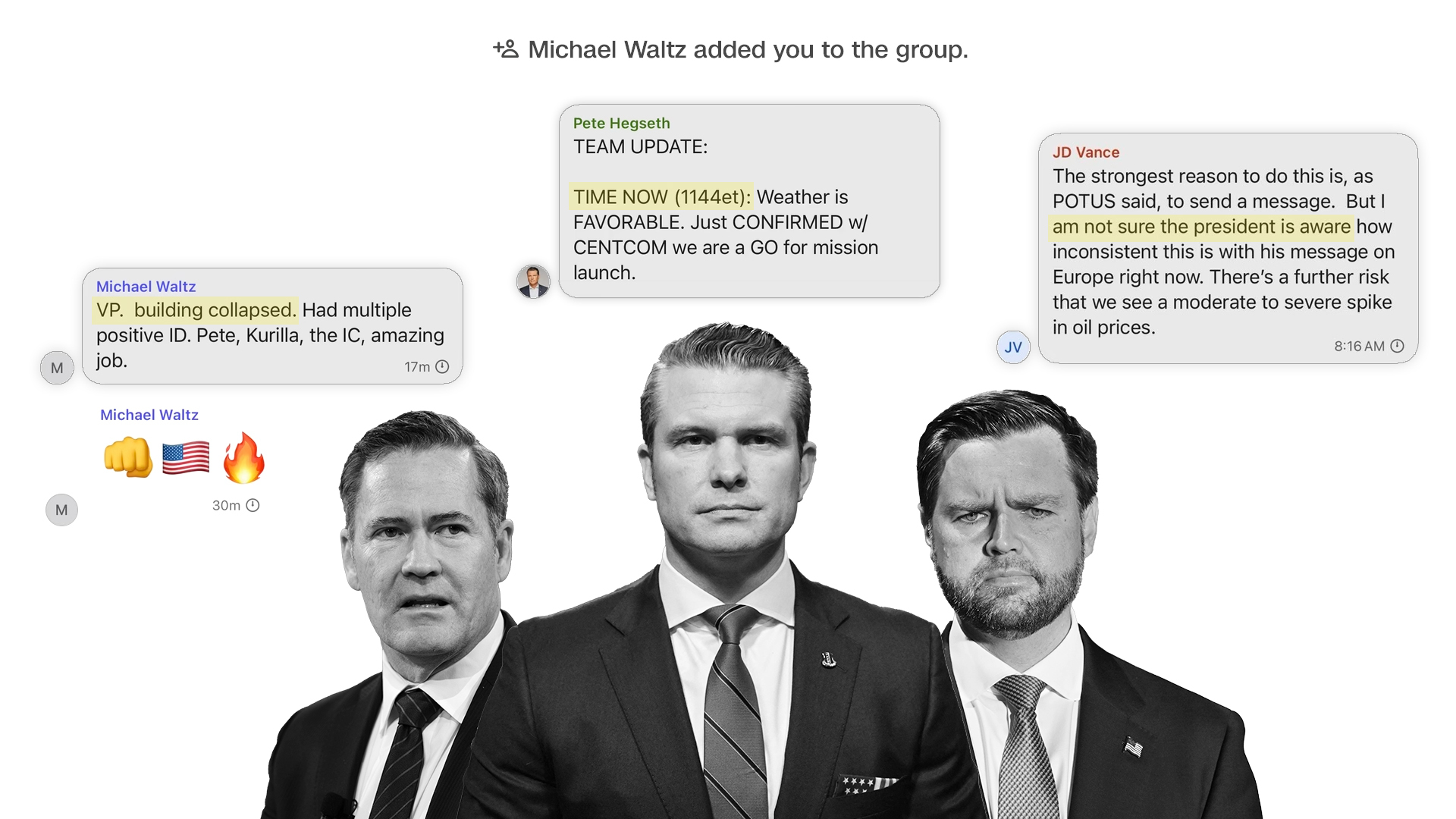
Signal, a free, open-source app championed by privacy advocates, journalists, and even some intelligence professionals, offers robust end-to-end encryption. However, even the most secure platforms can falter when human error enters the equation. A recent U.S. government Signal group chat, reportedly discussing potential military operations against the Houthis in Yemen, accidentally included journalist Jeffrey Goldberg, editor-in-chief of The Atlantic. This group included high-level officials such as Vice President JD Vance, Secretary of State Marco Rubio, and Secretary of Defense Pete Hegseth. The potential compromise of classified information — including troop movements, strategic targets, or operational timelines — poses a severe national security risk. Ironically, the adversaries being discussed, who also use Signal, now gain potential intelligence insight due to this operational lapse.
Encryption Alone Is Not Enough
This incident underscores a fundamental truth: even the strongest encryption is vulnerable to human mistakes. End-to-end encryption protects message content, but not against misdirected invitations, interface design flaws, or social engineering attacks. A single click can expose sensitive data, bypassing even the most sophisticated cryptographic defenses. Furthermore, while content is encrypted, metadata — such as who is communicating with whom and when — can still be exposed or inferred.
The Case for a Purpose-Built Government System
To address these vulnerabilities, the U.S. must invest in purpose-built, controlled communication systems — a “Zero-Fail Communication System” designed with national security and operational discipline at its core.. Building and maintaining such infrastructure is a significant undertaking, but the long-term security benefits far outweigh the upfront costs. These systems would incorporate layered security measures including biometric authentication, multi-factor authorization, hardware-based encryption, and real-time intrusion detection. A hardened operating system, specifically designed for secure communications, would further minimize attack surfaces. For ultra-sensitive data, air-gapped networks — physically isolated from the internet — offer critical protection.
Controlled Environments with Hybrid Architecture
While open-source security offers valuable transparency, a hybrid approach may be optimal for government use: audited open-source components deployed within tightly controlled, closed environments. Community auditing allows for broader scrutiny, while closed systems ensure strict access control and operational integrity.
Discipline and Protocol Are Non-Negotiable
Technology alone, however, is not enough. Comprehensive training, rigorous operational discipline, and human accountability must complement secure platforms. This includes background checks, security clearances, regular audits, and penetration testing to proactively identify vulnerabilities before adversaries do.
Strengthening Closed-Circuit Communication Protocols
One critical oversight in many private communication platforms is the lack of stringent user authentication and access control. Closed-circuit communication systems—especially those used for government or sensitive organizational operations—should never allow users to be invited freely without pre-established vetting mechanisms. For instance, access should be restricted only to users with verified credentials, such as a .gov or other official domain email address, or to those preloaded into the system as authorized participants.
It is both alarming and unacceptable that some platforms allow private communication rooms where any user can be invited without prior checks or oversight. This creates serious vulnerabilities in environments that require trust, accountability, and national security safeguards.
Drawing from military protocols—where I served as an Information Assurance Security Officer—users who violated communication best practices were immediately flagged. Their access to communication tools was suspended, they were retrained on proper usage, and only then was access reinstated. This wasn’t about punishment, but rather reinforcing the seriousness of secure communication practices. Civilian systems, particularly those used by public officials and government contractors, should adopt similar accountability models. When national trust and safety are at stake, the margin for error must be zero.
A Holistic Approach to National Security
In conclusion, the Signal incident serves as a stark reminder that secure communication is not solely a technological challenge — it's a human and operational one. The future of government communication lies in a holistic approach that blends dedicated, secure infrastructure with disciplined practices. When national security is on the line, there’s no room for a tap-happy finger or a single oversight to derail a mission.
It’s time for the U.S. government to invest in the next generation of secure communications — to protect its leaders, its data, and its citizens.
Explore Topics
Let's Create Something Amazing Together! Reach Out Now!
Join us on a creative journey. Contact us, and let's start discussing your unique project today!
